Overview
In this post I’m going to show how to use a pfSense virtual router in your VMware home lab. If you’re using a single flat network in your home lab, this post will introduce additional complexity, but I believe that this is a good thing in this case. It’s not often that you’re going to find an environment that only has a flat network using only the native VLAN. By using a virtual router such as pfSense, you’ll be able to mimic an environment that you’re likely to see in the real world. I’ve been using this set up for about five years now and while I occasionally run into issues because of the complexity, I can identify the issue and learn how to resolve it. Later I almost always see the same behavior in my job and am able to recognize it.
Some of the features of pfSense that I use are:
- VLANs
- Firewalling
- Spin up networks quickly
- Virtual IPs
- Load balancing
- Source and destination NAT
- DHCP
Here is an overview of pfSense from their website:
The pfSense project is a free network firewall distribution, based on the FreeBSD operating system with a custom kernel and including third party free software packages for additional functionality. pfSense software, with the help of the package system, is able to provide the same functionality or more of common commercial firewalls, without any of the artificial limitations. It has successfully replaced every big name commercial firewall you can imagine in numerous installations around the world, including Check Point, Cisco PIX, Cisco ASA, Juniper, Sonicwall, Netgear, Watchguard, Astaro, and more.
pfSense software includes a web interface for the configuration of all included components. There is no need for any UNIX knowledge, no need to use the command line for anything, and no need to ever manually edit any rule sets. Users familiar with commercial firewalls catch on to the web interface quickly, though there can be a learning curve for users not familiar with commercial-grade firewalls.
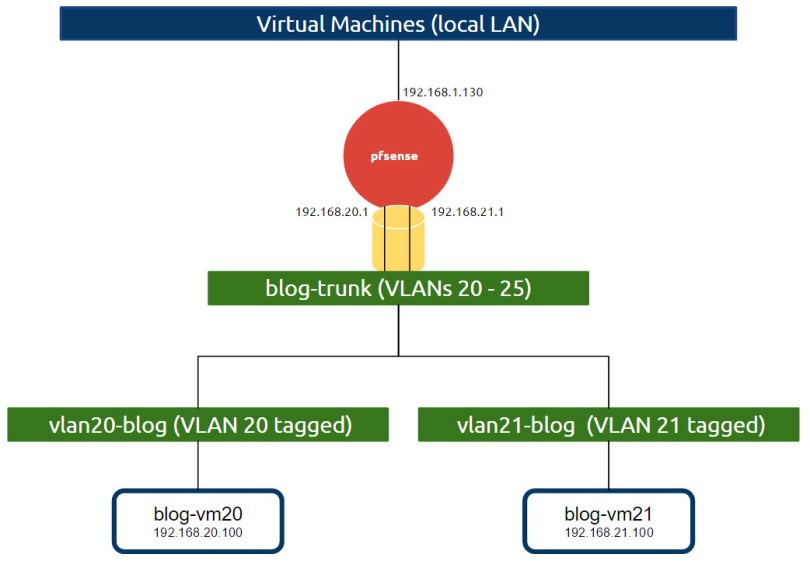
Here is an image of what I’ll show how to accomplish.
Download pfSense
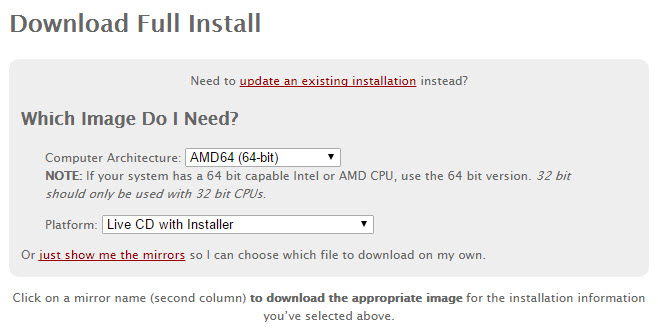
Download and select the latest stable version (version 2.2.6 at the time of this post). Choose the appropriate architecture and select the Live CD Installer:
Portgroup creation
Before we install pfSense we will create three portgroups in vCenter. You can of course name the portgroups whatever you’d like.
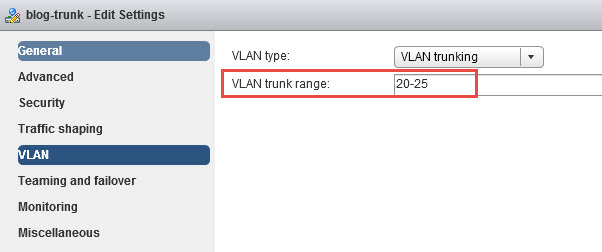
- blog-trunk
- VLAN type: VLAN trunking
- VLAN trunk range: 20 – 25 (or 20 – 21 is good enough for this exercise)
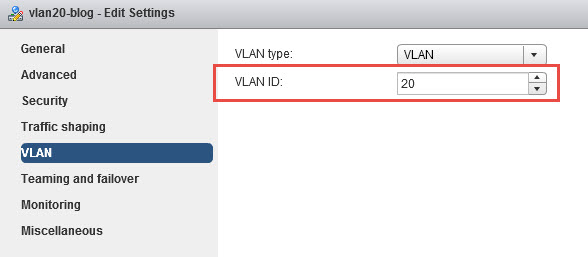
- vlan20-blog
- VLAN type: VLAN
- VLAN ID: 20
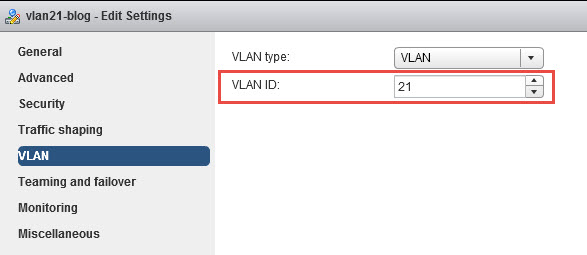
- vlan21-blog
- VLAN type: VLAN
- VLAN ID: 21
Installation
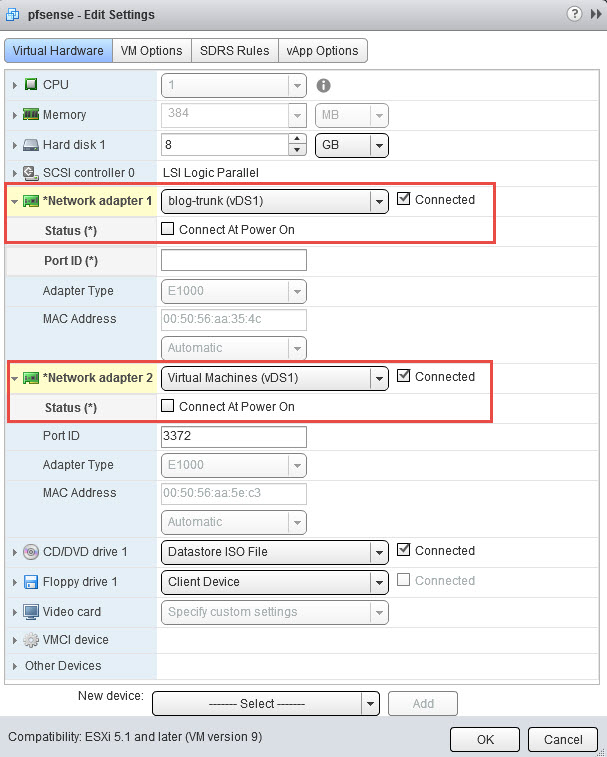
Create a VM in vCenter of type Other Linux (64-bit). I gave mine 1 vCPU and 384 MB of memory, but you can use whatever you think is appropriate. Give the VM two NICs. Connect the first NIC to the blog-trunk portgroup and the second to the Virtual Machines portgroup, which in my case is my LAN. Use the diagram above for reference. For reasons we will see later, set the NICs to not connect at power on. Lastly, configure the CD-ROM to use the pfSense ISO:
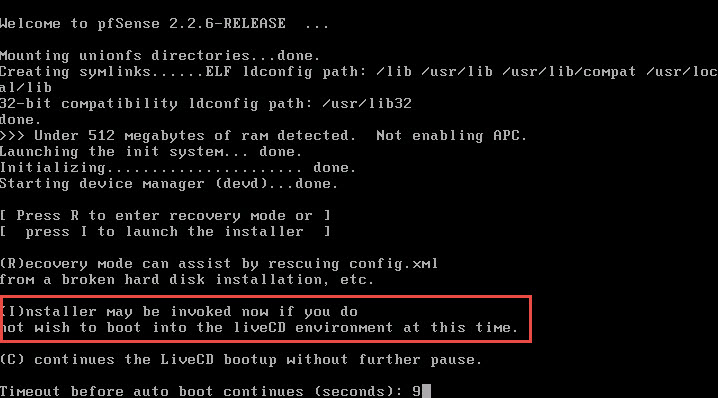
Boot the VM and open a console. Once you’re prompted to choose I(nstaller)… to install pfSense to the hard drive.
Select Accept these settings > Quick/Easy Install > Standard Kernel > Reboot
Here we can see why we booted the VM with the NICs disconnected. By default the LAN interface is set to 192.168.1.1, which is the same as my LAN’s default gateway.
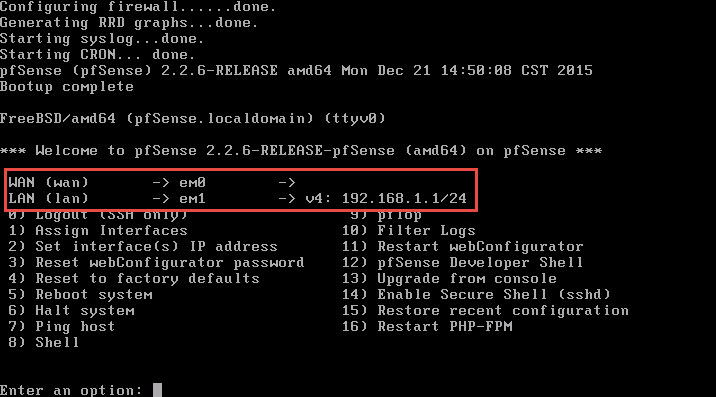
Select 2) Set interface(s) IP address. For this demonstration I set the following on the LAN (em1) interface:
- IP: 192.168.1.130
- Subnet: 255.255.255.0
- Gateway: 192.168.1.1
Choose to not enable the DHCP server on the LAN interface.
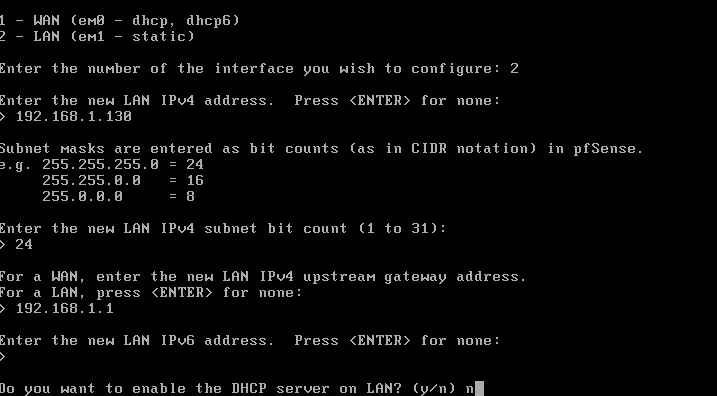
We won’t be configuring the WAN (em0) interface at this time. If prompted, choose not to reconfigure the web configrator port to use http unless you want to.
You can now reconnect the VM’s portgroups.
Configuring pfSense
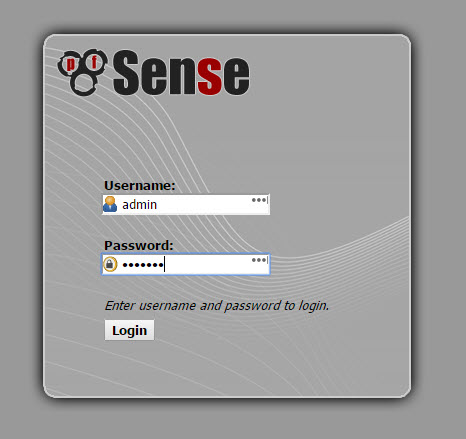
My pfSense’s web configuration page is available at https://192.168.1.130. The default usename and password are pfsense / pfsense.
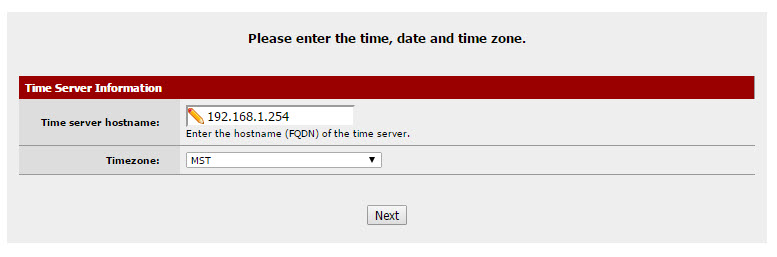
From here on out we will be setting up basic configuration values. Please substitute values as necessary.
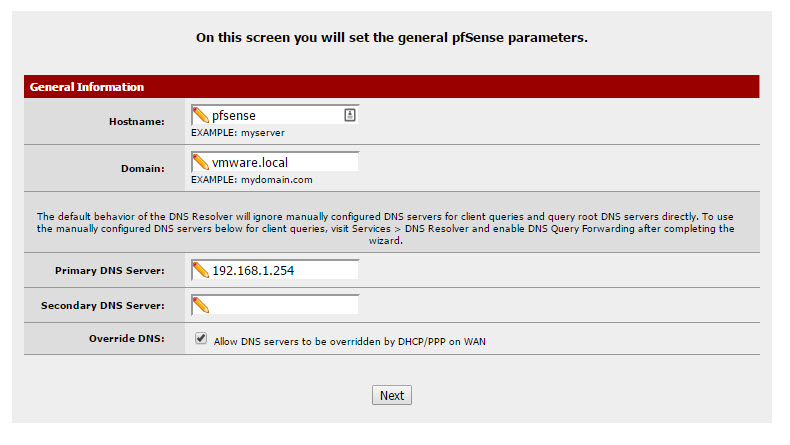
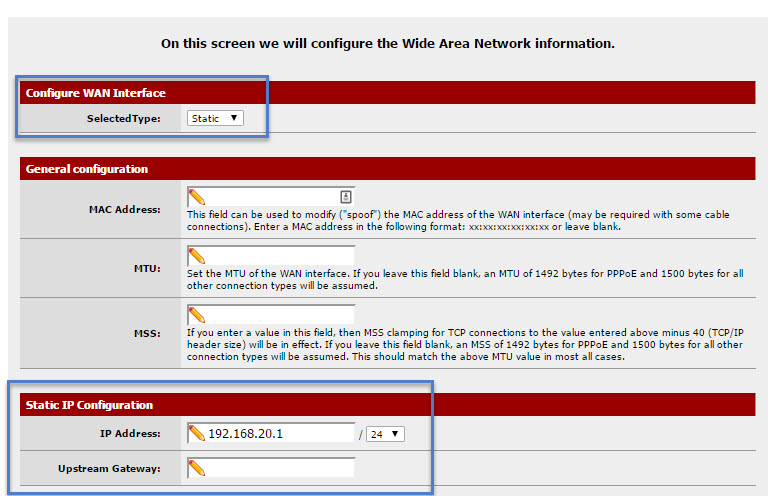
Configure the WAN interface
The WAN will actually be the internal side of the router that where your VMs will reside. In my lab I actually have this reversed, but this is easier for demonstration purposes. Feel free to swap your interfaces around to whatever makes the most sense to you.
Set the interface type to Static and set the IP to 192.168.20.1. Again, please consult the diagram above. This will be the first of possibly many “internal” interfaces/IPs assigned to the pfSense router and these networks are what you will use to place your VMs onto.
The LAN interface will already be set but you can change it here if you’d like:

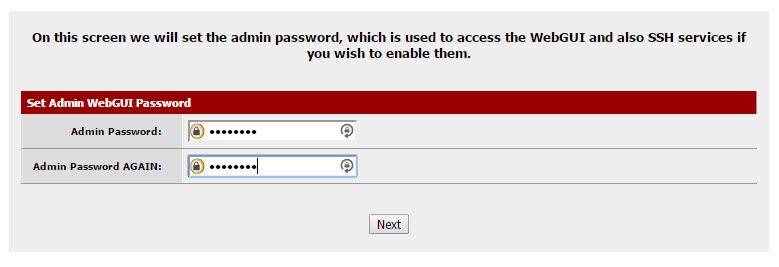
The last option is to change the default admin password:
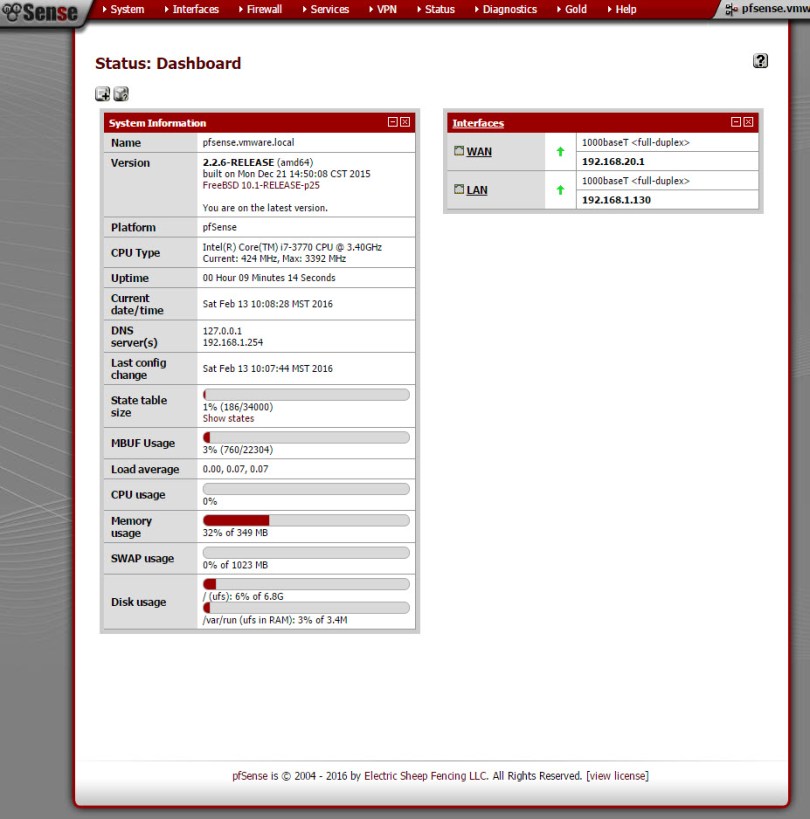
Once you’re finished you’ll be sent to the pfSense dashboard:
In part two I’ll show how to configure VLANs, firewalling and get some test VMs communicating on the network.
Hi there how many physical NICs are on your ESXi host? I am trying to achieve this set up but before i start would like to know if i can do this with one physical NIC as it is all i have on my ESXi host?
Some of my hosts have one and others have two. You should be able to do it with one NIC.